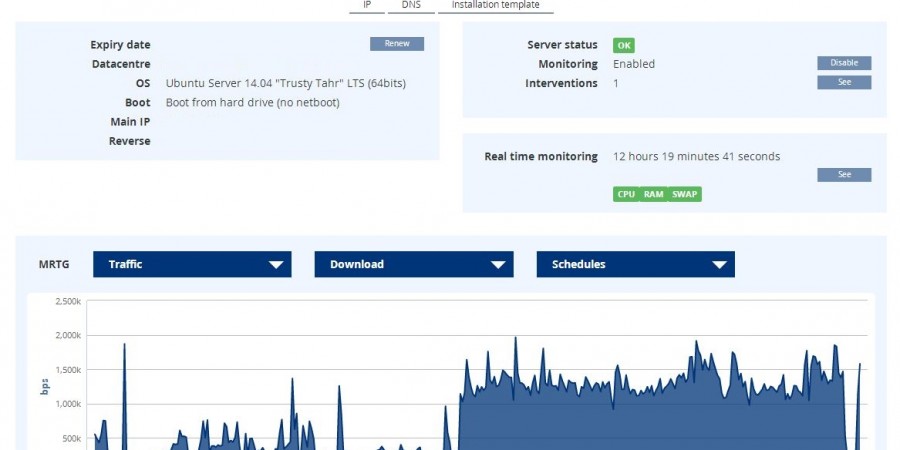
In something that has seemingly become an annual holiday tradition, I recently moved this WordPress site to a new hosting provider. This time I left was evicted from Oracle. I am always on the hunt for the absolute bargain option when it comes to hosting… but I also want my website to be decently performant. […]
FIRST – I am stealing code here and re-sharing (with very little modification). All credit goes the fine gentleman that wrote these two articles, I would urge you to read them: Bulk Add IP Access Restrictions to Azure App Service Using AZ Powershell Bulk Add Cloudflares IPs to Azure App Service Access Restrictions Using AZ […]
I had a recent requirement from one of our clients that took a little bit of tinkering to figure out… we will call our client Contoso LLC. and our project that we host for them we will call the “Cool Widget Project.” We built a really neat widget of an application for Contoso to use […]
Last year Google proposed marking any and all sites not using SSL in a negative fashion in its Chrome browser. This year they are indicating they plan on moving forward with this: Google Chrome gets ready to mark all HTTP sites as ‘bad’ To clarify what this means for small content creators… an extra ~$100+ […]
If you are looking for a quick way to install a LAMP (Linux, Apache, MySQL, PHP) stack on an Ubuntu server, this should take care of you: sudo apt-get install tasksel sudo tasksel install lamp-server mysql_secure_installation First command installs tasksel… which is a really handy program.